Home > Platform
Our External Attack Surface Management Platform
Observations
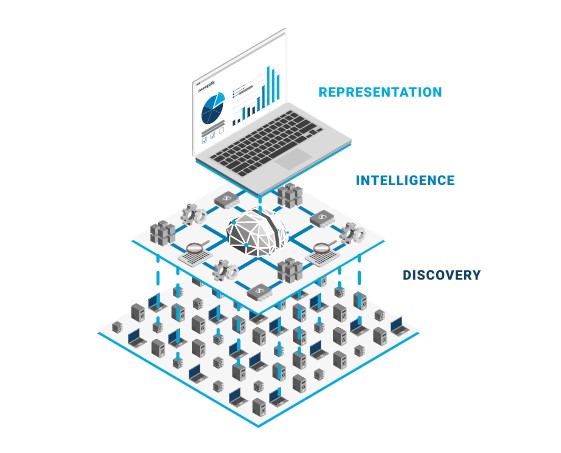
The intelligence layer of the Platform structures and prioritizes findings.
Assets
The Platform finds all internet-facing assets in the attack surface.
Events
The event-based architecture allows for performance and scalability.
How it works
Our cloud-based Platform builds an exhaustive dataset 24×7 about the organization’s attack surface based on advanced techniques.
A unique set of automatically and synergistically interacting data gathering, enrichment and artificial intelligence driven analysis modules are integrated into an event-driven platform architecture.
These modules coexist and feed each other data and information to yield a most complete, accurate and actionable dataset about an attack surface.
Features
How can you defend yourself if adversaries know your attack surface better?
Deep and complete
Non-intrusive, passive discovery from the infrastructure up to the data layer.
24×7 Automated intelligence
Continuous monitoring built around advanced reconnaissance techniques.
Actionable insights
Easy-to-remediate findings and insights with high impact.
Easy onboarding
Cloud-based SaaS not requiring any on-premise installation.
Benefits
Proactively protect your organization by augmenting your team with automated attack surface intelligence.
Better insights
Knowing what to protect based on actionable insights is key.
Less risk
Reducing your online exposure will eliminate intrusion options.
More time
Automation unburdens your security team.
Less damages
While guaranteeing a huge exposure reduction, we aim for zero.
Getting started
Four steps towards cyber resilience with the Sweepatic Platform.
1. Onboard
The Sweepatic Platform is activated in no time, needing only your primary domains.
2. Mimic the cyber attacker
Advanced techniques build an exhaustive and actual data set of your attack surface.
3. Draw insights
All internet-facing assets are analyzed and attack paths prioritized.
4. Take action
The Sweepatic Platform structures remediation actions, easy to ingest.
Collection of
Frequently Asked Questions
An EASM platform is a cloud-native solution that
continuously discovers, analyzes, and monitors everything connected to your company’s online exposure — domains, websites, hosts,
services, technologies, SSL certificates, etc. It provides real-time feedback on changes and issues occurring in the external attack surface of your organization.
Firstly, you get situational awareness of all changes in your online attack surface. You are the first to learn about any vulnerability or issue that may encourage bad actors to attack. Moreover, you reduce the risk of a cyberattack by finding and remediating vulnerable assets that your organization is using. In addition, an easy-to-operate solution, continuous scanning, and prioritized insights (“what to address first”) unburden your cybersecurity team, who get extra time for other tasks.
Contact us to learn all the benefits of the Sweepatic EASM Platform.
Sweepatic was founded in 2016 as one of the first in the Attack Surface Management field. The company is rapidly growing and appreciated for its innovative, user-friendly solution and expertise, among others, by Gartner, Cyber Security Made in Europe, Sibelga, Cegeka, and many other customers. What really makes us outstanding is our customer-first approach. Do you have a feature in mind or an integration request? We promise to help you out shortly.
Onboarding is quick and easy! You don’t need to install any software or agents. The platform is cloud-native and accessible by securely logging in via your internet browser.
Sweepatic applies a “zero-knowledge approach,” meaning the only information the platform requires to start is either a company name or a primary domain.
Maintaining a complete and accurate scope definition is very important. Hence, Sweepatic enables customers to complete their scope, at all times, by suggesting new primary domain candidates, importing additional IP addresses, etc.
We would love to hear from you. In the main menu, navigate to the company and then the contact section.
Request your Trial version
We offer you the opportunity to test our External Attack Surface Management platform with all functions and without restriction. This way you can form an objective opinion and experience the advantages of such a security tool as a component for your cyber security concept in live operation.
Test it now – without obligation and free of charge!



